

Why list a select 15 abstainers in the summary rather than the 14 voting against? Besides the obvious ones (Israel, US, Czechia), there’s Hungary, Argentina, Paraguay, Papua New Guinea, Fiji, Palau, Nauru, Malawi, Tuvalu, Tonga and Micronesia.


Why list a select 15 abstainers in the summary rather than the 14 voting against? Besides the obvious ones (Israel, US, Czechia), there’s Hungary, Argentina, Paraguay, Papua New Guinea, Fiji, Palau, Nauru, Malawi, Tuvalu, Tonga and Micronesia.


Call them Li-Ion batteries to prevent confusion with lithium batteries such as CR-2032, which probably have been used in pagers.


Overloaded Li-Ion batteries don’t reliably explode. I would have expected them to place the explosive inside an oversized battery pouch along with a heating element in series with the battery. A microcontroller on the board could go short-circuit upon receiving a certain message, making a large current flow through the heating element and triggering the explosive.


Well, I’m guessing they concealed them in an extra-large Li-Ion battery and wired a heating element in series inside it, so that shorting the terminals by the circuitry triggered the explosive. Pagers use so little power that the lower capacity would be hard to notice and the heating element’s voltage drop would be negligible. I assume the pagers’ command & control equipment had backdoors, too.


@kurcatovium@lemm.ee


Not in the egg compartment, of course, but most other places will do.


Trojan is any malware that pretends to be a legit program. It does not need to have backdoor or info stealing capability even though most malware (trojan or not) today does. For example, pre-Internet trojans might just invisibly install themselves along the actual program they were bundled with and then nuke the system on a certain date. Antivirus companies would even advance the date on their systems in hopes of detecting these and being the first to develop a patch.
But since this program is not malicious, it just straight up hogs system resources and/or crashes it due to a mistake, it cannot be considered malware and therefore not a trojan.
Certain Intel processors from around 2000 would crash everything when loading the 4 bytes F0 0F C7 C8 into a specific register. Would you consider this a backdoor because it allows any program to crash the system? I wouldn’t say so, crashing Windows 98 was probably not too hard anyway…


I installed FakeStore and set the app’s installed_by* property from Package Manager to FakeStore (com.android.vending, the same as Google Play Store), which was enough to fool the public transport app I’m using. Is this the workaround you’re talking about, or does it require MicroG too?
* Not what it’s actually called, can’t remember that


It’s the apps that prevent themselves being sideloaded. Presumably, their devs will enact similar policy on EU iOS too.
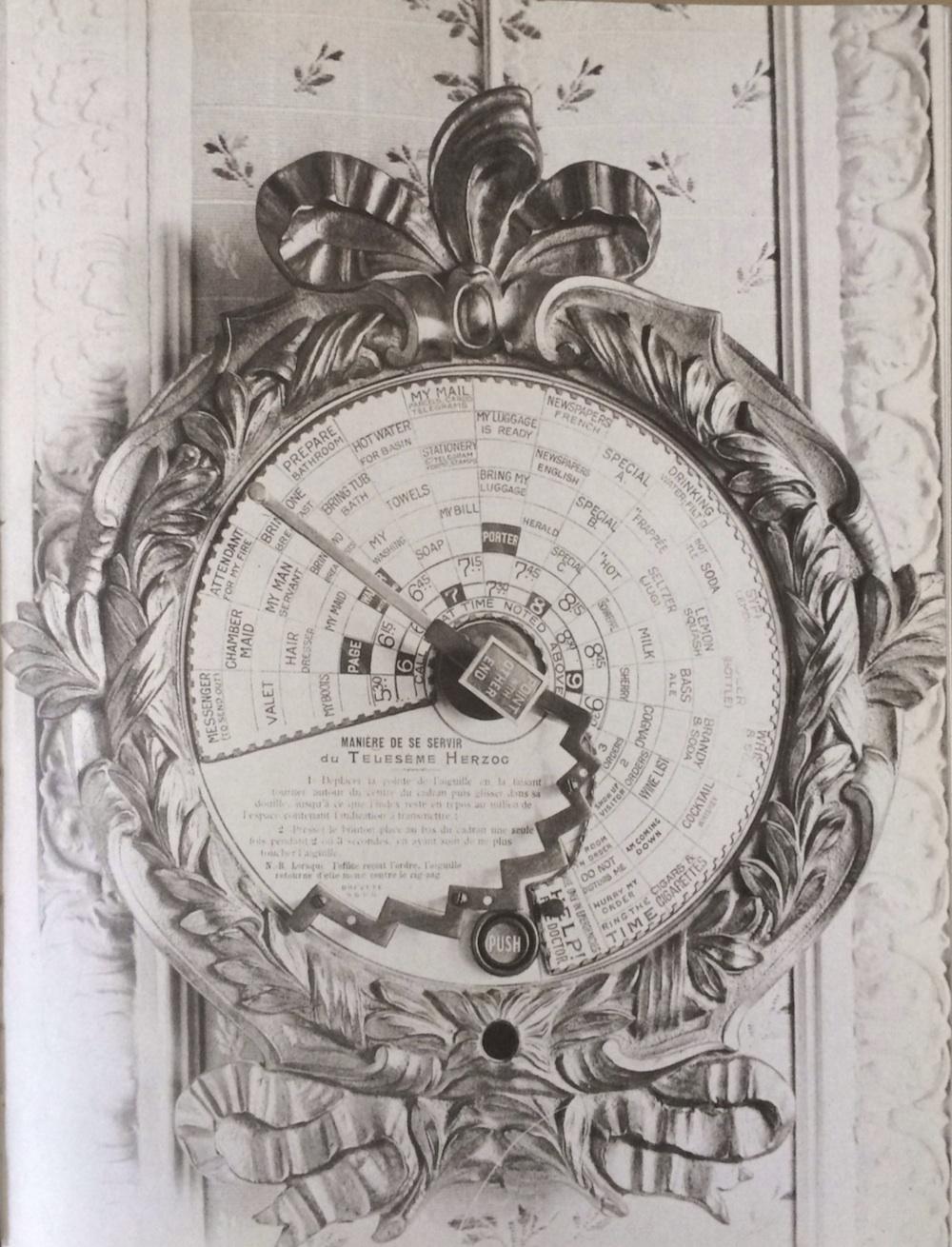
ATTENDANT
FOR MY FIRE
I wonder what it does, as the HELP (FIRE/DOCTOR) field is elsewhere. Light my cigar? That would make more sense next to CIGARS & CIGARETTES.


It was advertised as “2 TB (64 GB Extended)” at a local clearance sale (not AliExpress), which was basically correct though I would prefer “64 GB but misprogrammed so everything can get corrupted at any time”. When buying it, I didn’t yet know if I could reprogram the chip but the low price was justified for the pretty aluminum case with a USB-C port and place for a custom PCB. I decided to buy it also to prevent another, less technical person from using it and losing their data. The store was getting rid of inventory for very cheap and would close soon so no more fake drives would be ordered.


Well, depends on how much you’re OK with some problems. I knowingly bought a “2 TB (64 GB Extended)” flash drive, tested its sectors and reprogrammed it to 32-in-64-GB for wear leveling and bad sector avoidance because it was still a cheap 32GB USB drive. I made sure to label it for “non-critical use” such as movies.
As for camping lanterns, ones charged from mains might have a nasty habit of shocking their users. (The YouTube channel contains a huge number of cheap Chinese charger teardowns and most don’t meet safety criteria. Usually, there is just 1 or 2 layers of thin tape between mains and the output you can touch.)


Sometimes, counterfeits or unknown brands are so similar to the real deal that it barely matters. I’d say that basic electronics (alarm clocks, kitchen scales, calculators, SD security cams) or even RAM is fine. With appropriate expectations, parts like video or USB cables, hubs etc., small home improvement items (hooks, screws) are fine too. Avoid categories where a lot of items have fake specs (storage devices, LED bulbs, anything that claims a runtime on a Li-Ion battery). Power electronics (especially if using mains or non-tiny Li-Ion batteries) can be downright dangerous. For novelty items and electronics modules, it’s usually easy to find text or video reviews on other websites because they’re easy to uniquely describe. Remember to consider ways in which the product can be utter crap despite high reviews citing good first impressions; it also helps to have practical knowledge of testing the properties of the items and fixing common issues.


Well, then you’re going to hear
most of the time, much like Spotify.
(Last time I was in a Spotify-“enhanced” waiting room was 6 years ago so no idea if that still holds.)

Explains why chicken feed has been disappearing but the traps keep closing “empty”.


Thanks; I thought “his town hall” meant that the town’s administrative building (Rathaus) was named after Trump.


Yes but you’ll need to intercept the HDMI cable with a beefy microcontroller to turn it back on when displaying patient data again so you don’t get fired. At this point, I’d be looking to disable the corresponding software if the computer is accessible.


…Like MS-DOS getting open sourced. It’s pretty much worthless unless you need to use some really old device.
When I try to outset a polygon but it’s clockwise:
Yup. Israel is treating them like land that’s free to colonize, when in reality a nation (albeit one with unstable government, and only recently UN-recognized) lives there.
Similarly, Japan can’t claim it’s “defending itself” if it hypothetically performs violent acts in Lebanon.