Then explain why my good doggo gets little gifties! Check and mate.
- 0 Posts
- 9 Comments
The GPL states that its text must not be modified. I take this to mean (though I’m no lawboy), that if you wanted to have a license with the same terms plus some changes (the butthole rule), you would have to rewrite the whole thing. It would not nearly be a “GPL license”.
This is very important nitpicking I’m doing here, okay?

 14·20 days ago
14·20 days ago… Jack is a nickname for John?
Godot can be used for any app, not just games. (Same goes for the other engines, I assume.) Though I can’t say if you would have an easier time picking it up, rather than the traditional Java or Kotlin route.

 2·23 days ago
2·23 days agoAt some point M$ allowed the free download of something called “Windows XP Mode for Windows 7”. It was some virtual machine or something. What matters is that it’s possible to extract an XP ISO from this, which I have successfully used to spin up a virtual machine! It still complains about a license key, though.
The reason I mention this is that this is still available on archive.org, and it’s signed by M$, so you know it’s legit. I don’t know if other ISOs available have such a receipt of authenticity. Probably, but I never cared enough to check, especially since I grabbed this from the official website while it was available.
 17·26 days ago
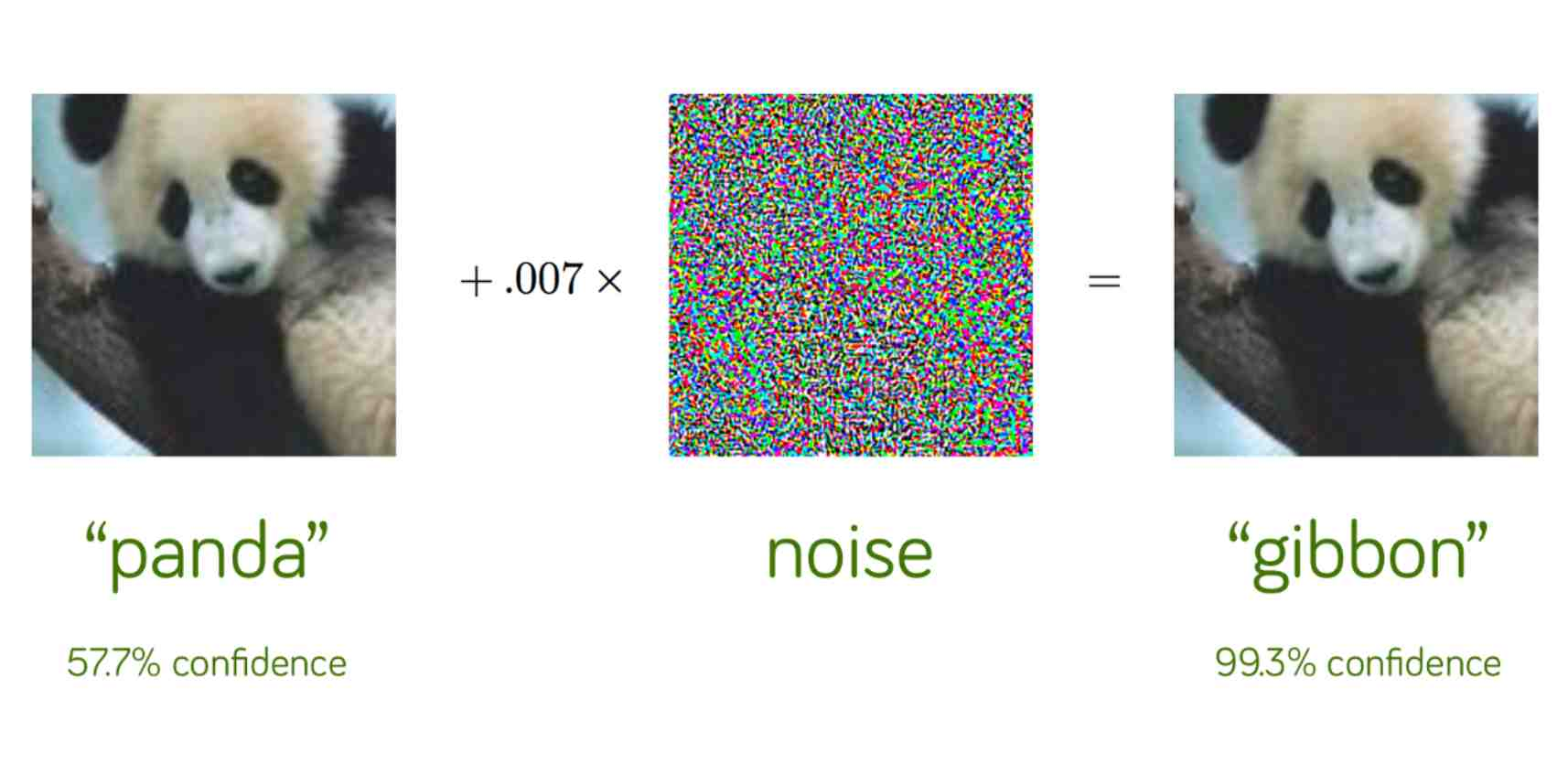
17·26 days agoIt’s possible to manipulate an image in a way that the original and the new one are indistinguishable to the human eye, but the AI model gives completely different results.
Like this helpful graphic I found
Or… edit the HTML…

 31·1 month ago
31·1 month agoIf the clients only communicate through the server, then without prior knowledge of one another, such as gpg keys, no.
Otherwise, maybe they could both generate an RSA key. Then they would both encrypt a string of this format “<RANDOM_STRING>_<RSA_PRIVATE>”, and send that to the other. After receiving the other’s package, each one sends over their own private key. They can use this to decrypt the string, which both of them had chosen before knowing what the other had. They can use the string to decide who won based on predetermined rules.
I put the private key in the package because this way clients can check that it was in fact the key used to encrypt it in the first place. Faking that would require infinite computing power or quantum shenanigans, I suspect.
Also this is probably way overkill and has flaws I didn’t think of.

 7·2 months ago
7·2 months agoI took it as a chance to weed them out. I went through each one manually and made a choice whether to keep it. Went from ~260 to 130.
I also unsubbed from each so as to make yt unusable, so I wouldn’t be tempted to go there, unless specifically looking for something.

Why does this look and sound like the inspirational scene of a Mockumentary?