Arthur Besse
cultural reviewer and dabbler in stylistic premonitions
- 85 Posts
- 215 Comments

 0·17 days ago
0·17 days agoi guess maybe if you’re using a device with a tiny screen and a lemmy client that doesn’t let you zoom in on images

 3·17 days ago
3·17 days agoIt’s literally a covert project funded by google to both sell pixels and harvest data of “privooocy” minded users. It seems to be working well.
Is it actually funded by Google? Citation needed.
I would assume Graphene users make up a statistically insignificant number of Pixel buyers, and most of the users of it I’ve met opt to use it without any Google services.

 0·18 days ago
0·18 days agoshoutout to the person who reported this post with “Reason: Bot meme, you can’t even read it. whoever replies is a bot too” 😂

 16·19 days ago
16·19 days agoYou may not like it, but this is what peak performance looks like.

 5·2 months ago
5·2 months agoxzbot from Anthony Weems enables to patch the corrupted liblzma to change the private key used to compare it to the signed ssh certificate, so adding this to your instructions might enable me to demonstrate sshing into the VM :)
Fun :)
Btw, instead of installing individual vulnerable debs as those kali instructions I linked to earlier suggest, you could also point debootstrap at the snapshot service so that you get a complete system with everything as it would’ve been in late March and then run that in a VM… or in a container. You can find various instructions for creating containers and VMs using debootstrap (eg, this one which tells you how to run a container with
systemd-nspawn; but you could also do it with podman or docker or lxc). When the instructions tell you to rundebootstrap, you just want to specify a snapshot URL likehttps://snapshot.debian.org/archive/debian/20240325T212344Z/in place of the usual Debian repository url (typicallyhttps://deb.debian.org/debian/).

 26·2 months ago
26·2 months agoA daily ISO of Debian
testingor Ubuntu 24.04 (noble) beta from prior to the first week of April would be easiest, but those aren’t archived anywhere that I know of. It didn’t make it in to any stable releases of any Debian-based distros.But even when you have a vulnerable system running sshd in a vulnerable configuration, you can’t fully demo the backdoor because it requires the attacker to authenticate with their private key (which has not been revealed).
But, if you just want to run it and observe the sshd slowness that caused the backdoor to be discovered, here are instructions for installing the vulnerable liblzma deb from snapshot.debian.org.

 7·2 months ago
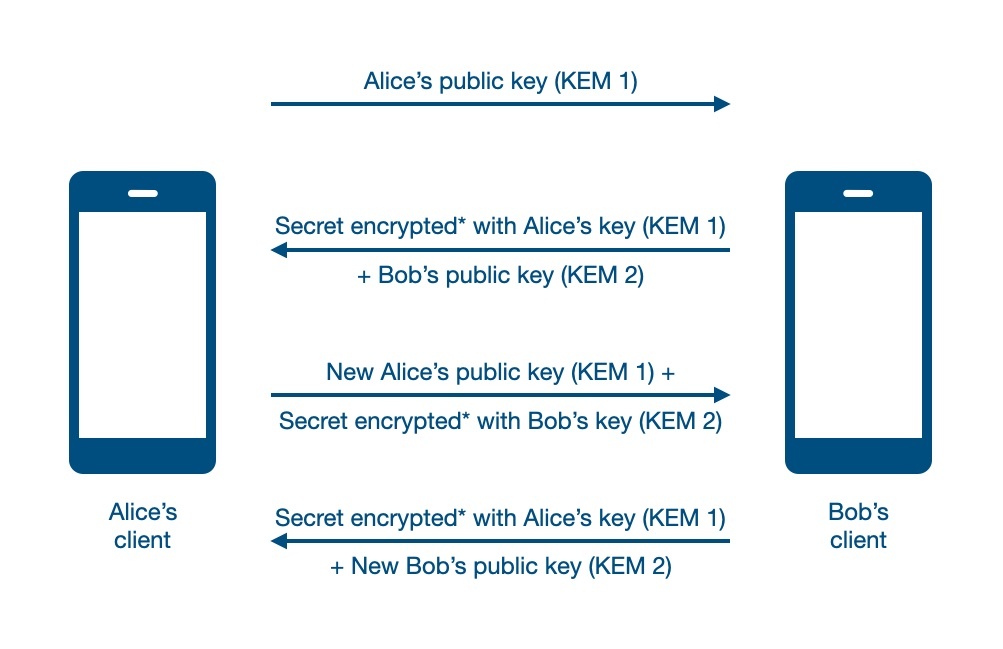
7·2 months agoMattermost isn’t e2ee, but if the server is run by someone competent and they’re allowed to see everything anyway (eg it’s all group chat, and they’re in all the groups) then e2ee isn’t as important as it would be otherwise as it is only protecting against the server being compromised (a scenario which, if you’re using web-based solutions which do have e2ee, also leads to circumvention of it).
If you’re OK with not having e2ee, I would recommend Zulip over Mattermost. Mattermost is nice too though.
edit: oops, i see you also want DMs… Mattermost and Zulip both have them, but without e2ee. 😢
I could write a book about problems with Matrix, but if you want something relatively easy and full featured with (optional, and non-forward-secret) e2ee then it is probably your best bet today.

 203·2 months ago
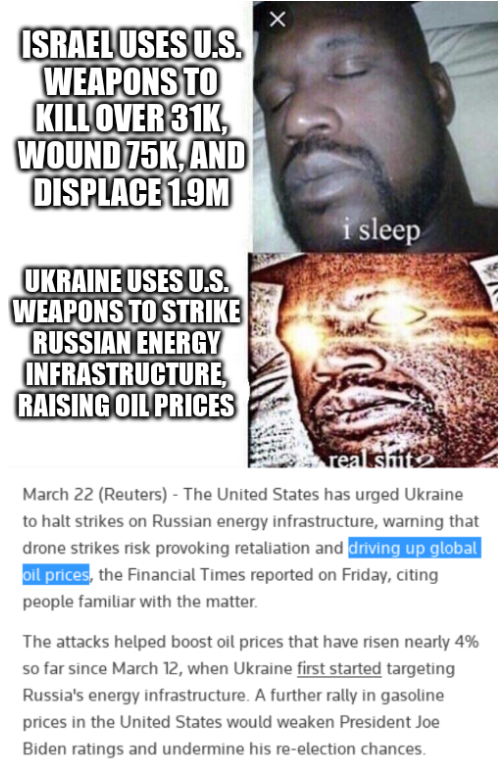
203·2 months agoyou don’t see any downside to nuclear escalation?

 7·2 months ago
7·2 months agoWho is we???
Perhaps OP is a member of the US congress, trying to figure out what to vote for? 🤪
There is a nice sample of Michael Parenti talking about this kind of use of the word “we” at the beginning of this song. (lyrics here)

 53·2 months ago
53·2 months agothe US didn’t have to coerce them to kick him out.
You think the $4.2B IMF loan package they got 30 days before his expulsion wasn’t contingent on revoking his asylum? Here is evidence that it was, two months before it happened.
He essentially got kicked out for installing spyware and listening devices into the embassy’s private network.
What? The listening devices and hidden cameras were in fact installed by the Spanish private security company who was ostensibly working for the embassy but who it turned out was also working for the CIA, for the purpose of spying on Assange (including in the bathroom, where he would go to meet with his lawyers due to his suspicion that the other rooms had been bugged), as has been well documented in both US and Spanish courts:

 141·2 months ago
141·2 months agoWhat is it that people in the UK don’t understand about ‘indeterminate detention without charge’?
He was detained without charge for many years, but there are charges now: the US unsealed their 2018 indictment against him immediately after they coerced Ecuador into revoking his asylum in April 2019, and they added more charges a month later.
As the linked article explains, he is currently charged with 17 counts of espionage and 1 count of conspiracy to commit computer intrusion. He remains in His Majesty’s Prison Belmarsh while fighting the US’s extradition request.
See also https://en.wikipedia.org/wiki/Indictment_and_arrest_of_Julian_Assange

 2·2 months ago
2·2 months ago

 2·2 months ago
2·2 months agoOk, you and @d3Xt3r@lemmy.nz are both mods of /c/linux@lemmy.ml now. Thanks!

 7·3 months ago
7·3 months agoOk, I just stickied this post here, but I am not going to manage making a new one each week :)
I am an admin at lemmy.ml and was actually only added as a mod to this community so that my deletions would federate (because there was a bug where non-mod admin deletions weren’t federating a while ago). The other mods here are mostly inactive and most of the mod activity is by me and other admins.
Skimming your history here, you seem alright; would you like to be a mod of /c/linux@lemmy.ml ?

 61·3 months ago
61·3 months agoAs of today, NixOS (like most distros) has reverted to a version slightly prior to the release with the Debian-or-Redhat-specific sshd backdoor which was inserted into xz just two months ago. However, the saboteur had hundreds of commits prior to the insertion of that backdoor, and it is very likely that some of those contain subtle intentional vulnerabilities (aka “bugdoors”) which have not yet been discovered.
As (retired) Debian developer Joey Hess explains here, the safest course is probably to switch to something based on the last version (5.3.1) released prior to Jia Tan getting push access.
Unfortunately, as explained in this debian issue, that is not entirely trivial because dependents of many recent pre-backdoor potentially-sabotaged versions require symbol(s) which are not present in older versions and also because those older versions contain at least two known vulnerabilities which were fixed during the multi-year period where the saboteur was contributing.
After reading Xz format inadequate for long-term archiving (first published eight years ago…) I’m convinced that migrating the many projects which use XZ today (including DPKG, RPM, and Linux itself) to an entirely different compression format is probably the best long-term plan. (Though we’ll always still need tools to read XZ archives for historical purposes…)

 6·3 months ago
6·3 months agofor those unfamiliar: Reflections on trusting trust by Ken Thompson

 62·3 months ago
62·3 months agomaybe it’s important to note he isn’t on trial for treason? The charges are for hacking and espionage.
He isn’t on trial for treason in courts of law, but he is in the court of public opinion - various commentators and some officials (including Senator Joe Lieberman and then-CIA Director Mike Pompeo) have used the word to describe his publishing.
















If you’re ready to break free of Android, I would recommend https://postmarketos.org/ though it only works well on a small (but growing!) number of devices.
imho if you want to (or must) run Android and have (or don’t mind getting) a Pixel, Graphene is an OK choice, but CalyxOS is good too and runs on a few more devices.